What Buyers Need
Visible identity, review, and recovery controls
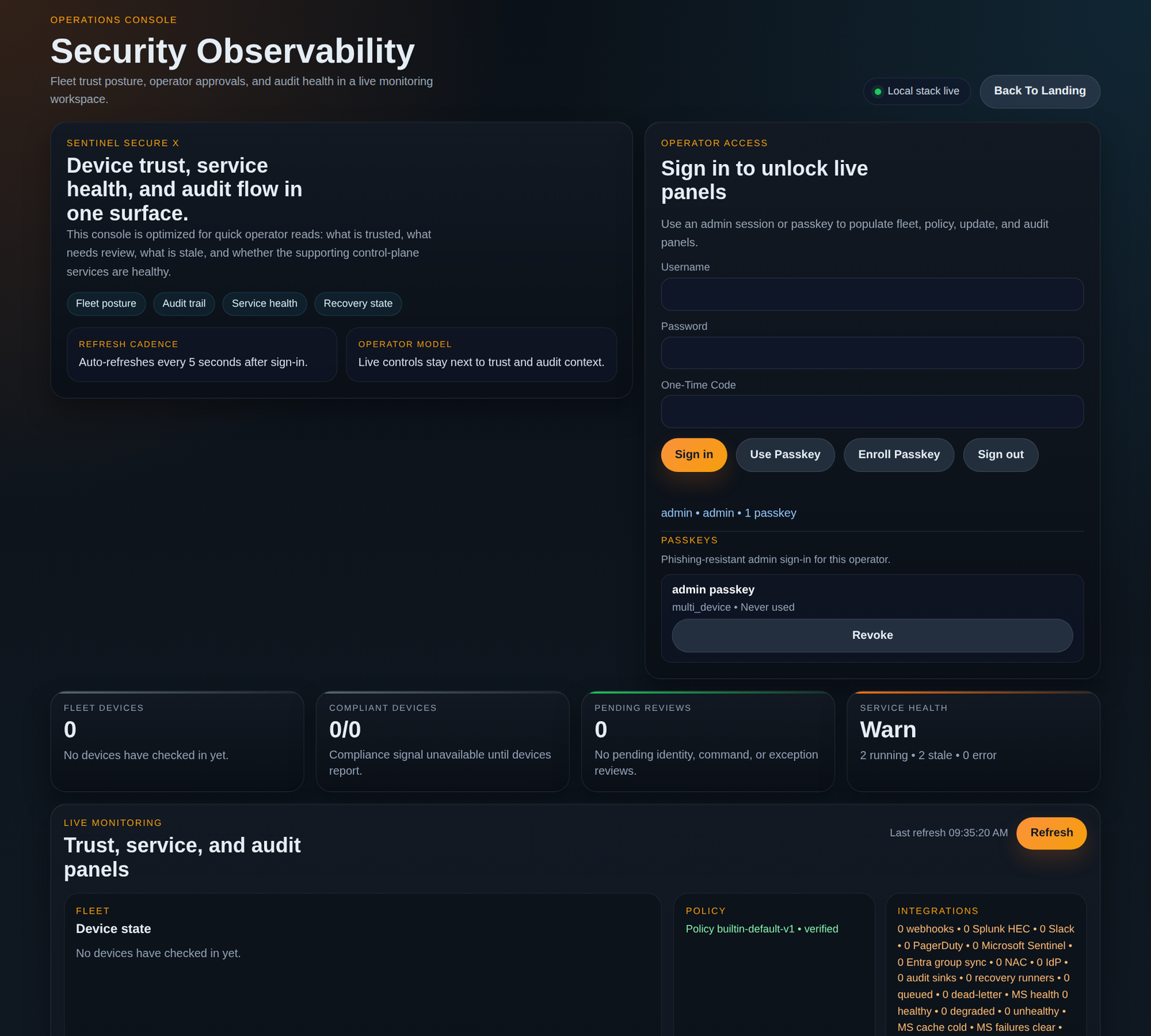
Sentinel Secure X
Continuous Device Trust Control Plane
Buyer-Ready Device Trust
Sentinel Secure X combines certificate-bound identity, attestation visibility, operator approvals, signed updates, and recovery governance in one console, so buyers can inspect a living trust model instead of taking security claims on faith.
Buyers do not only ask whether a device can connect. They ask whether it stays trustworthy now, whether risky actions are reviewable, and whether recovery preserves accountability.
Fleet Overview
Identity
Certificate-bound
Attestation
Reviewed
Recovery
Governed
Device
edge-gateway-14
Trust Tier
Managed
Approval State
Approved
Update State
Staged Safely
Cert Status
Valid
Pending Review
2 sensitive actions
Recent Audit
Identity promotion approved
Signed update staged
Diagnostic command awaiting approval
Built For High-Assurance Teams
The page now leads like a buyer site, but it stays honest: no invented logos, no inflated ROI claims, just clear buyer-fit signals.
Agent Downloads
Linux, macOS, and Windows agent packages are published with checksum metadata so operators can grab the exact artifacts that match this deployment and verify integrity before rollout.
Linux
Includes the Python endpoint agent, Linux unit templates, and a rendered preview service file.
Download Linux BundlemacOS
Includes the endpoint agent, launchd helpers, and a rendered plist preview for Mac operators.
Download macOS BundleWindows
Includes the endpoint agent, PowerShell service scripts, and the Windows-oriented sample config.
Download Windows BundleMetadata
Use the manifest and checksum list to confirm archive names, sizes, and SHA-256 fingerprints.
Why Buyers Switch
The hard part is rarely proving that a device connected once. The hard part is proving who controls it, how trust changes are reviewed, and what happens when identity, policy, or recovery needs to change later.
Buyer Question
Certificate-bound identity, attestation state, and approval context stay visible, so trust can be re-evaluated instead of assumed.
Buyer Question
Commands, policy exceptions, and certificate actions can move through review paths, with distinct approvers for sensitive steps.
Buyer Question
Audit trails, service health, delivery status, and signed exports make the decision trail available for inspection.
Buyer Question
Updates, rollback, and recovery stay inside governed workflows, so resilience reinforces trust instead of bypassing it.
Product View
The product story is strongest when buyers can picture the workflow: device shows up, trust is reviewed, sensitive actions are governed, updates are staged, and recovery never leaves the audit trail.
Identity stays anchored to certificates
Enrollment, rotation, and approval all stay visible to operators.
Policy is tied to actual operations
Commands and exceptions are controlled where teams make decisions.
Recovery becomes part of trust
Rollback and restore paths are designed before the incident arrives.
What Feels Premium
Landing page messaging now gets to value, fit, and proof faster before asking a buyer to click deeper.
What Feels Different
The page leans into certificate review, attestation, updates, and recovery, which is more specific than typical zero-trust marketing.
What Supports The Sale
The CTA still takes buyers straight into the product surface where the trust story can be demonstrated live.
Real Product View
This image was captured from the live local dashboard after sign-in. It gives buyers a concrete product surface to anchor the story: fleet status, audit visibility, service health, and operator controls in one place.
Trust Narrative
01
Only certificate-authenticated devices enter the system, and new identities can wait for approval.
02
Attestation evidence, device state, and approval context stay visible before trust is elevated.
03
Commands, exceptions, and certificate actions move through guardrails instead of ad hoc admin action.
04
Operators can inspect fleet state, integration delivery, background services, and audit integrity together.
05
Rollback, recovery jobs, and signed evidence preserve trust even when the system is under pressure.
Who This Fits
Sentinel Secure X is strongest where a device mistake turns into a customer problem, an audit finding, or a safety concern. It gives security, platform, and operations teams a shared operating story.
Show how managed endpoints remain governed after deployment, not just at onboarding.
Keep identity, updates, and recovery reviewable even when devices are distributed and hard to touch.
Bring approval discipline and audit evidence to systems where failure handling has real-world cost.
Give customers a visible, defensible trust model instead of a black-box service promise.
Why It Resonates
The page now distinguishes Sentinel by showing trust governance and recovery discipline, not just access control language.
Why It Converts Better
Buyers can understand the promise, inspect the product shape, and move into the dashboard without getting lost in technical prose.
Why It Feels Credible
The page avoids made-up customer proof and instead uses inspectable workflow language that matches the product.
Ready To Inspect The Product
Start on the dashboard for live fleet status, operator sign-in, audit events, and service health.